The headlines are bleeding with the same tired narrative. Iran claims over 30 of its universities were hit by sophisticated cyberattacks. They point the finger at the usual suspects—the United States and Israel. The media laps it up, framing it as a David vs. Goliath digital showdown.
They are looking at the wrong map.
This isn't a story about a sudden surge in digital warfare. It’s a story about the failure of state-sponsored infrastructure and the convenient use of "cyber-aggression" as a blanket excuse for internal systemic decay. If you believe the narrative that these attacks are unprecedented or even particularly effective, you’ve fallen for the oldest trick in the geopolitical book: the externalized scapegoat.
The University as a Soft Target Fallacy
Most "analysts" treat a university network like a high-security vault. In reality, academic institutions are the digital equivalent of a sieve. They are designed for openness, data sharing, and remote access. When Iran claims 30 universities were "attacked," what they are actually saying is that 30 poorly maintained, underfunded networks—running on pirated software and outdated patches—had their vulnerabilities exploited.
I’ve seen state departments scramble to explain why their internal databases are leaked on Telegram. They never say, "We forgot to update our server." They say, "We were targeted by an elite foreign intelligence unit."
Calling these incidents "attacks" gives them a level of prestige they don’t deserve. Most of the time, it’s not a Stuxnet-level operation. It’s a script kiddie using a leaked exploit because the IT department at a provincial university hasn't updated its firewall since 2018. The "sophistication" is a lie told to protect the jobs of the people who failed to secure the perimeter.
The US-Israel Response: Strategic Silence vs. Calculated Leaks
The competitor article focuses on the "ready response" of the US and Israel. This is a fundamental misunderstanding of how signals intelligence works. Real cyber warfare doesn't announce itself with a press release.
When the US or Israel actually wants to degrade Iranian capabilities, they don't go after the chemistry department’s student records at a mid-tier university. They go after the SCADA systems controlling centrifuges or the command-and-control nodes of the IRGC.
The "response" mentioned in mainstream reports is often just standard diplomatic posturing.
- The US strategy: Plausible deniability coupled with "defend forward" doctrines.
- The Israeli strategy: Direct kinetic-cyber integration that aims for physical results.
If a university website goes down, it’s noise. If the power grid in a military sector flickers, that’s a signal. By conflating the two, Iran manages to inflate its status as a victim of "global powers," while the West gets to look like it’s constantly looming over Tehran’s shoulder. Both sides win the PR war. The truth loses.
Why 30 Universities? The Numbers Game
Why 30? Why not 5 or 500? The number is large enough to sound like a crisis but small enough to seem manageable. In the world of cybersecurity, "30 universities" is a statistical rounding error.
Every single minute, every public-facing IP address in Iran (and the US, for that matter) is being probed, scanned, and "attacked" by automated bots. If we used the Iranian government’s definition of a cyberattack, every high schooler with a copy of Kali Linux is a state-sponsored threat actor.
The nuance missed by the lazy consensus is the intent vs. capability gap.
- Intent: To project strength through victimhood.
- Capability: High enough to detect the probes, but too low to actually stop them.
Iran’s domestic internet—the "National Information Network"—was supposed to be their Great Firewall. It was meant to insulate them from the "decadent" global web. These university breaches prove that you can’t build a digital fortress when your citizens are constantly looking for tunnels out. The use of VPNs by students and faculty creates massive backdoors that no state-level firewall can close.
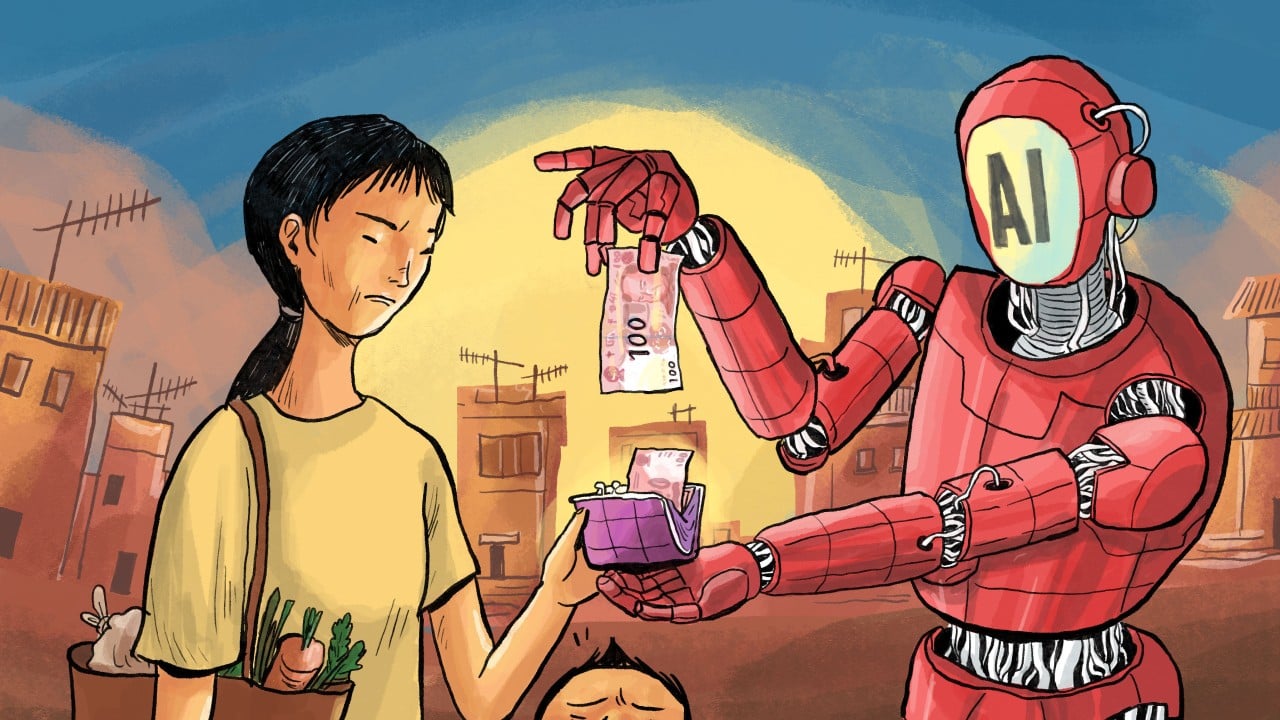
The Economic Reality of Digital Defense
Let’s talk money. Cybersecurity is a rich man’s game.
The US spends billions on its Cyber Command. Israel’s Unit 8200 is a literal factory for the world’s most elite security startups. Iran, strangled by sanctions, cannot legally buy the enterprise-grade hardware and software required to defend a modern network.
They are fighting a 2026 war with 2012 tools.
When you can't buy the latest Cisco hardware or Palo Alto software updates, you rely on "indigenous solutions." In tech, "indigenous" is often code for "reverse-engineered and buggy." This isn't a knock on Iranian engineers—who are some of the most resourceful in the world—it’s a cold reality of the supply chain. You cannot defend against a zero-day exploit using a cracked version of Windows Server.
The Truth Nobody Admits: Cyber-Pessimism
The contrarian truth is that these attacks are likely not even coordinated.
We are living in an era of Cyber-Pessimism, where we assume every glitch is a ghost in the machine sent by a foreign power. It is far more likely that these 30 universities were hit by various independent actors—hacktivists, ransomware gangs, and bored teenagers—and the Iranian government simply bundled them together to create a narrative of a "coordinated Western assault."
It’s a brilliant move. It shuts down internal dissent. If a student protests, they are a "digital collaborator." If a server fails, it’s "foreign sabotage."
Stop Asking "Who Did It?"
People always ask, "Was it the Mossad? Was it the CIA?"
That is the wrong question. The right question is: "Why does it matter?"
If the data stolen is academic research that was already destined for publication, or student emails about cafeteria food, the "attack" is a non-event. We have been conditioned to see every breach as a catastrophe. In the hierarchy of national security, the integrity of a university’s library database is near the bottom.
The real danger isn't the hack itself. The danger is the normalization of the excuse. When a state can blame its internal failures on an invisible digital enemy, it no longer has to be accountable to its people.
The Actionable Reality
If you are an organization watching this play out, don't learn the "lesson" the media is selling. Don't go out and buy more "anti-hacking" software.
- Segment your networks: The reason one "attack" hit 30 universities is likely because they shared infrastructure or authentication protocols.
- Assume breach: Don't build a wall; build a system that functions while being actively robbed.
- Kill the ego: Iran’s mistake is making this a matter of national pride. Security is a matter of hygiene.
The "response" from the US and Israel wasn't "prepared"—it was inevitable because the vulnerabilities were so glaring. You don't need a complex plan to walk through an open door.
Iran will continue to claim victimization. The West will continue to shadow-box. And 30 universities will continue to run on hope and outdated kernels. The cycle isn't breaking because the cycle is useful for everyone involved. Except, of course, for the people whose data is actually sitting on a dark web forum right now.
Stop looking for the masterminds. Start looking at the patch notes.